Kaspersky APT Intelligence Reporting
Exclusive and timely insights into high profile cyber-espionage campaigns
![]()
Sorry, this product is no longer available, please contact us for a replacement.
Overview
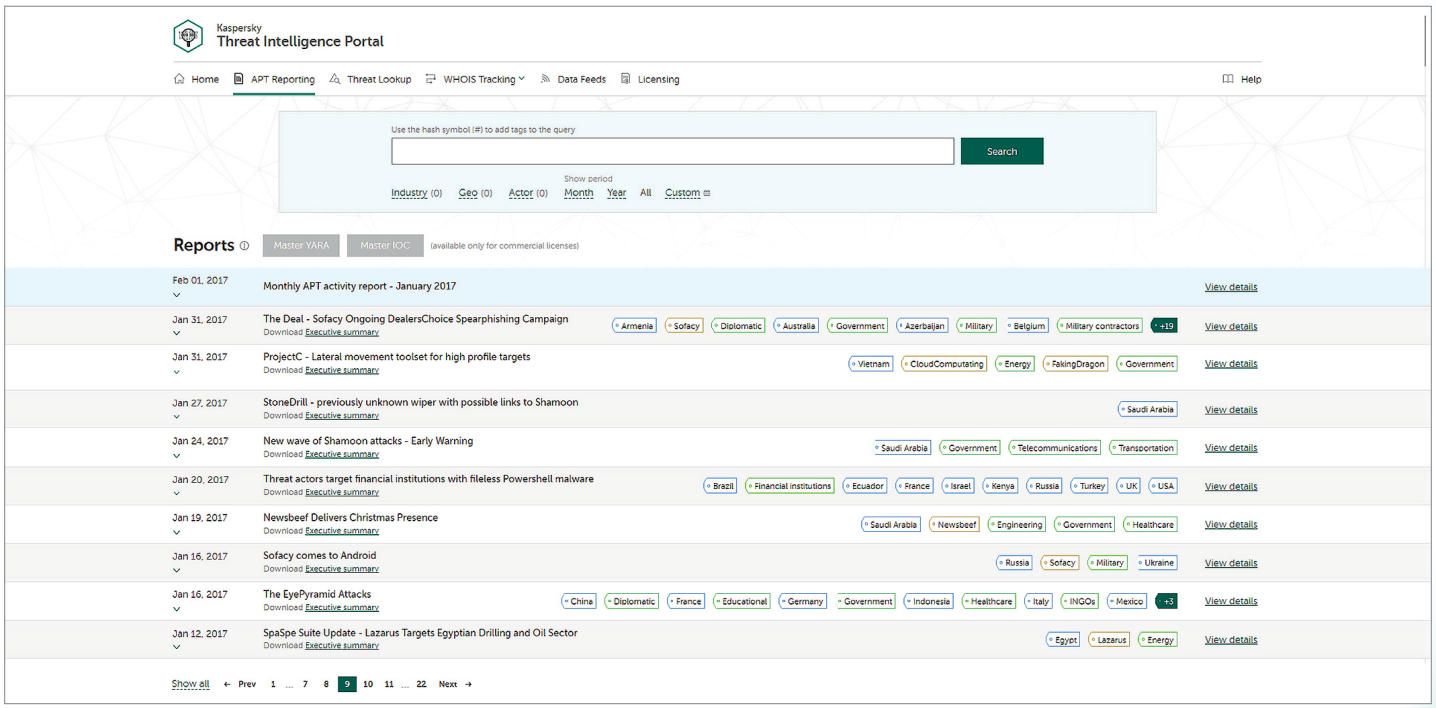
Increase your awareness and knowledge of high profile cyber-espionage campaigns with comprehensive, practical reporting from Kaspersky. Leveraging the information provided in these reports, you can respond quickly to new threats and vulnerabilities – blocking attacks via known vectors, reducing the damage caused by advanced attacks and enhancing your security strategy, or that of your customers.
Kaspersky has discovered some of the most relevant APT attacks ever. However, not all Advanced Persistent Threat discoveries are reported immediately, and many are never publicly announced. Be the first to know, and exclusively in the know, with our in-depth, actionable intelligence reporting on APTs.
As a subscriber to Kaspersky APT Intelligence Reporting, we provide you with unique ongoing access to our investigations and discoveries, including full technical data, provided in a range of formats, on each APT as it’s revealed, including all those threats that will never be made public.
![]()
Insights into the most damaging threats
Kaspersky Lab's GReAT team now tracks 200+ threat actors, uncovering the most sophisticated and dangerous targeted attacks, cyber-espionage campaigns, major malware, ransomware and underground cybercriminal trends in 85 countries
![]()
Access to non-public investigations
Only a small number of our investigations are announced publicly but all are reported to our active customers, helping them to proactively deploy effective threat detection and risk mitigation controls for the associated campaigns
![]()
Content relevant to your specific role
Each report provides an overview of the campaign, outlining industries and regions affected, probably attribution and objectives, as well as detailed technical analysis with a list of corresponding IoCs and YARA rules
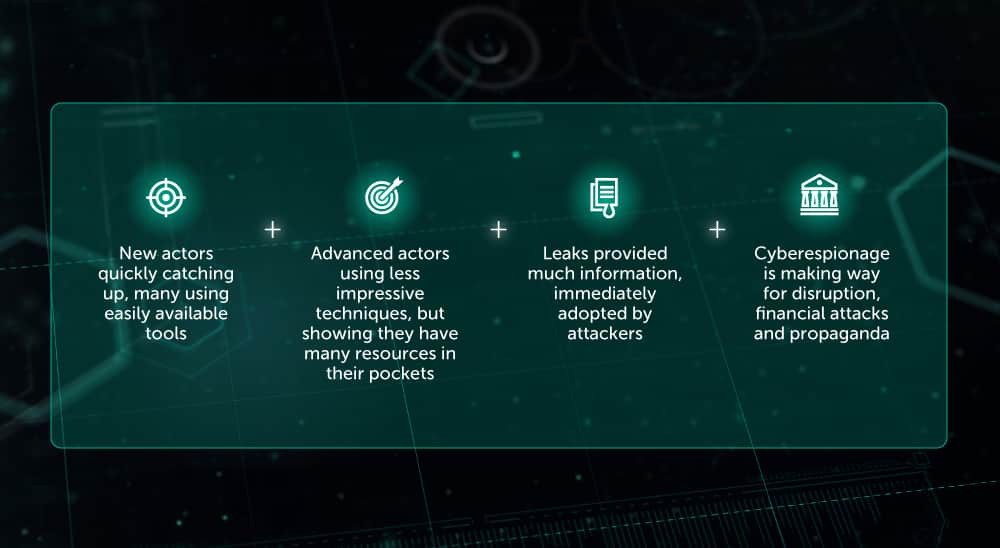
The Risk
Tracking, analyzing, interpreting and mitigating constantly evolving IT security threats is a massive undertaking. Enterprises across all sectors are facing a shortage of the up-to-the-minute, relevant data they need to help manage the risks associated with IT security threats, due to:
Suitable for
Kaspersky APT Intelligence Reporting is ideal for:
- Enterprise
- Financial Services
- Managed Security Service Providers
Pricing Notes:
- Pricing and product availability subject to change without notice.